How (and Why) to Develop Incident Response Playbooks
What is an Incident Response Playbook?
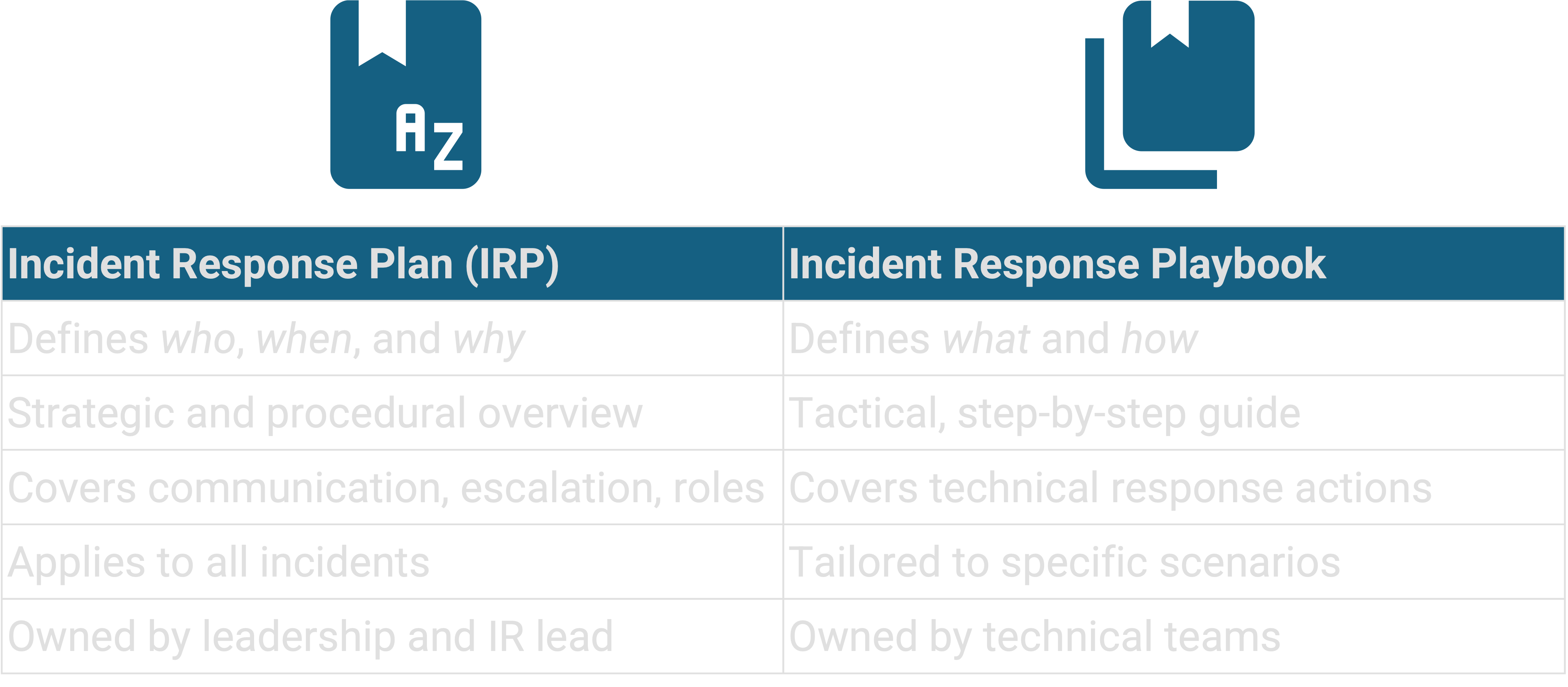
Anyone who’s experienced an incident knows: during security incidents, there’s rarely time to think. The pressure is high, the clock is ticking, and every decision has consequences. This is when many organisations discover that just having an IRP isn’t enough. The plan outlines who does what and when, but it doesn’t explain how those actions should actually happen. That’s where your IR playbooks come in.
An IR playbook is a structured, step-by-step guide for handling a specific incident scenario. It translates the intent of your IRP into clear, repeatable actions for your team. Each playbook defines exactly what to do when you detect an event such as phishing, credential theft, data loss, or malware infection.
Where the IRP provides governance, escalation paths, and high-level procedures, the playbook dives into execution. It specifies what data to collect, which systems to isolate (if possible, and how to do so safely), who to notify, and when to escalate. In short, the IRP gives you the framework, the playbook tells you the moves.
Together, they form the backbone of a resilient response capability: the plan ensures coordination and authority, while the playbook ensures precision and speed.
Why Playbooks Matter
Without playbooks, most IR relies on experience, improvisation, and memory. That might work in a small environment with a single incident responder, but in a growing organisation it quickly leads to problems:
- Different analysts take different approaches to similar events
- Important evidence is lost because no one knew to collect it
- Containment steps are delayed while people debate approvals
- External communications are inconsistent or incomplete
Playbooks solve these problems by establishing structure. They standardise response actions, clarify responsibilities, and reduce the cognitive load during high-pressure situations. This consistency not only improves response time but also supports accountability and regulatory compliance.
Imagine a mid-sized organisation that suffers a business email compromise (BEC). A senior executive’s mailbox is accessed by an attacker who sets up forwarding rules and sends fraudulent payment instructions to the finance team.
Without a playbook, the IT staff might disable the account but forget to search for other compromised users, review forwarding rules, or preserve mailbox logs for investigation. Finance might not be informed in time to stop the transfer, and legal might only hear about it days later.
A well-constructed playbook would guide responders through the full process: confirming the compromise, preserving evidence, resetting credentials, checking mail rules, verifying financial transactions, and notifying legal, HR, and management. Each step is defined, owned, and time-bound.
This level of preparation can be the difference between a controlled incident and a costly breach.
How Frameworks Support Playbook Development
Several recognised frameworks provide a foundation for building playbooks that align with industry standards and best practices:
NIST Cybersecurity Framework (CSF) places playbook development within the Respond and Recover functions. Playbooks directly support the Response Planning, Mitigation, and Improvements categories by defining how to contain and eradicate threats.
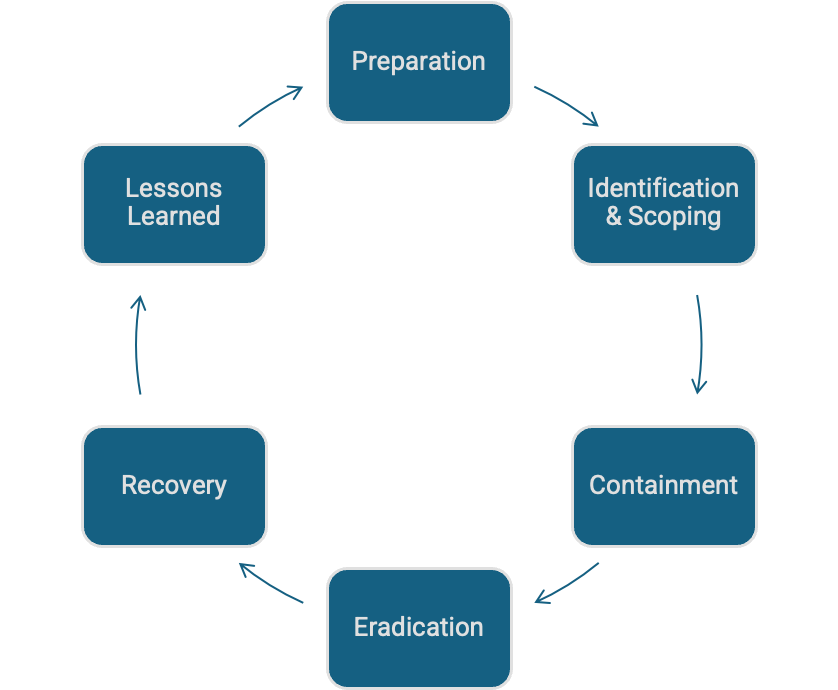
SANS PICERL (Preparation, Identification, Containment, Eradication, Recovery, Lessons Learned) is almost tailor-made for playbooks. Each playbook naturally follows this flow, ensuring a complete lifecycle approach.
MITRE ATT&CK offers a detailed mapping of attacker tactics, techniques, and procedures (TTPs). Using ATT&CK helps you link your detection and response actions to real-world adversary behaviour and ensures your playbooks cover relevant techniques.
Building playbooks that reflect these frameworks improves operational quality and also demonstrates alignment with widely accepted security standards; something that can help during audits or insurance reviews.
How to Build Effective Playbooks
Like most IR processes, developing IR playbooks should be an iterative process. Start small, focus on your most likely threats, and expand as your maturity grows.
Step 1: Select High-Likelihood Scenarios
Begin with two or three incident types your organisation is most likely to face. For most mid-sized organisations, phishing-based credential theft, malware infection, and accidental data exposure are good starting points. You can later add more complex scenarios such as insider threats or supply chain breaches.
Step 2: Identify Inputs and Triggers
Determine what initiates the playbook. This could be a SIEM alert, an EDR detection, a helpdesk ticket, or a user report. Your playbook doesn’t have to have a sing that will inform the investigation: system logs, network captures, email headers, or threat intelligence.
Step 3: Define Containment and Eradication Steps
Map the exact actions required to contain the incident and remove the threat from your environment. These steps should reflect your actual environment and tools. For example:
Disable affected user accounts or endpoints in Active Directory or MDM
Block malicious domains on the firewall or proxy
Quarantine infected machines in the EDR platform
- Be specific: “Use Defender for Endpoint to isolate the host” is better than “Isolate the system”
Step 4: Document Decision Points
Identify moments where a decision must be made, i.e. whether to isolate an entire network segment or engage external IR support. Document who is authorised to make those calls and under what circumstances. This prevents confusion and delays during an active incident.
Step 5: Define Communication Steps
Outline how information should flow during the incident. Who needs to be notified, in what order, and by what means? Include templates for internal updates, management / executive / board briefings, and external notifications to regulators, partners, government departments, or law enforcement. Many breaches worsen because communication lags behind containment.
Step 6: Assign Roles and Responsibilities
Every task in the playbook should have an owner. Use a RACI (Responsible, Accountable, Consulted, Informed) matrix to clarify expectations. A typical playbook might involve:
- Analyst: triage alerts, collect logs, and perform containment
- Incident Lead: coordinate activities, track progress, and escalate decisions
- Legal or Privacy Officer: handle regulatory and contractual obligations
- Communications Team: manage internal and external messaging
Step 7: Validate Against MITRE ATT&CK
Cross-check your playbook against relevant ATT&CK techniques. For instance, if you’re creating a phishing playbook, verify that your detection and response steps align with techniques like T1566.001: Spearphishing Attachment and T1059: Command and Scripting Interpreter. This ensures your team can recognise and respond to the tactics actually used by adversaries.
Step 8: Test and Refine Through Exercises
Run the playbook in a tabletop or simulated environment. Walk through each step and identify where clarity, dependencies, or tools are lacking. Capture lessons learned and refine the document accordingly. Playbooks must evolve over time, reflecting changes in technology, staff, and threat landscape, and should cover the PICERL stages:
Best Practices for Effective Playbooks
Keep them concise and usable. The best playbooks are short; one or two pages focused on key actions, not lengthy prose. During a crisis, no one will read a ten-page manual. Checklists are a fantastic tool that keep things simple and actionable.
Balance technical and procedural steps. Include both the hands-on actions (e.g. collect logs, isolate systems) and the business processes (e.g. notify executives, engage counsel).
Ground them in reality. Base every step on capabilities you actually have. A playbook that references a SOAR platform or EDR tool you don’t use is just fiction; unhelpful in a real-world incident and creates false confidence.
Control and maintain versions. Store playbooks alongside your IRP in a secure repository. Track revisions and authorship, and ensure only authorised personnel can modify them. Keep both digital and physical copies of the latest versions of these documents; don’t assume your Sharepoint or Confluence repo will be available during an incident.
Review after every major change or incident. Each new incident provides insights that can refine playbooks. Update them after lessons-learned sessions, tool upgrades, or organisational changes.
Integrate automation where feasible. As your capabilities mature, identify repetitive steps, such as host isolation, hash lookups, or IOC blocking, that you can automate through your EDR or SOAR platform. Automation doesn’t replace the playbook; it makes it faster and more reliable.
Consider a phishing credential theft scenario. A staff member reports a suspicious email that looks like a Microsoft 365 login prompt. The security analyst follows the phishing playbook:
- Verify the email header and confirm the domain is malicious
- Check for other recipients and block the sender in Exchange
- Use logs from the identity provider to identify logins from unexpected geographies
- Force password resets for affected users
- Search for suspicious MFA enrolments or token reuse
- Notify legal and HR if personal data exposure is suspected
- Document findings, impact, and remediation steps
- Conduct a short awareness reminder for staff
Following a tested playbook ensures nothing is missed, and everyone, from analyst to executive, knows their role.
Turning Plans into Practice
An IRP defines your process, but playbooks make it operational. They remove ambiguity, speed up action, and create consistency across the organisation. They are, in essence, your IRP in motion.
Start small: choose one or two common scenarios and document your response in detail. Test them in a tabletop exercise with your IT, security, and management teams. Capture lessons, refine, and expand from there.
Over time, you’ll build a library of playbooks that not only guide your technical response but also strengthen coordination across departments. Each exercise will make the team faster, calmer, and more effective when real incidents occur.
In the next article of this series, we’ll look at how to test your incident response capability through tabletop exercises, using those playbooks to simulate real-world events, reveal gaps, and turn preparation into confidence.
Disclaimer: This content may have been edited or refined with assistance from AI tools. All final content, views, and recommendations are our own.
