Top 10 DFIR Predictions for 2026: Incident Response Trends to Watch
Incident response has changed over the last few years. AI began replacing human analysts rather than augmenting or working alongside them (decidedly ill-advised, at least for now), cloud forensics went from niche to normal, and ransomware operations continued to become disturbingly professional. Security teams learned painful lessons about coordination, preparedness, and the value of having a tested plan rather than a dusty PDF.
Next year, DFIR will mature further. Organisations will move from reactive firefighting toward structured readiness and resilience. The focus will shift from responding well to preventing chaos in the first place. From real-world consulting work and engagements with clients preparing for, or recovering from, serious incidents, here are our 10 predictions for the next 12 months.
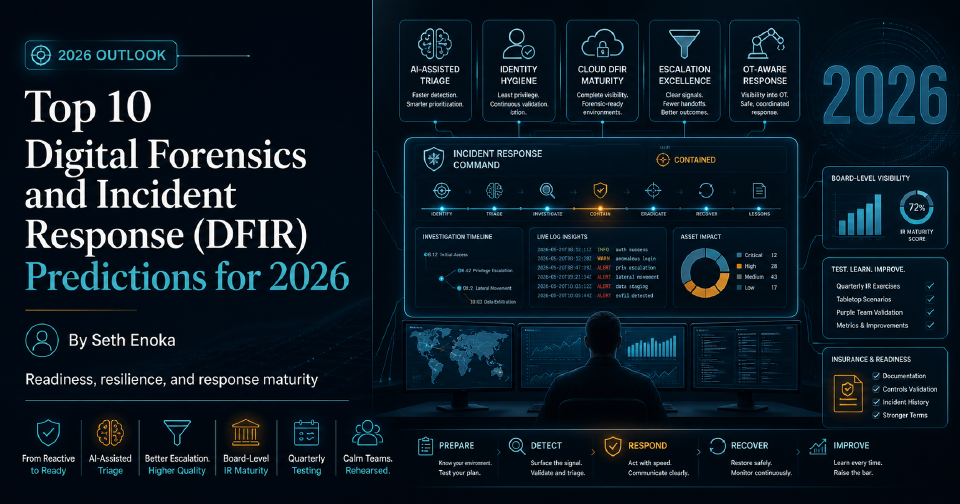
Quick Answer: The Biggest DFIR Trends for 2026
The biggest digital forensics and incident response trends for 2026 aren’t just technical. They’re operational:
- Incident response moves from emergency support to readiness roadmaps
- AI-assisted triage becomes normal, but human validation remains decisive
- SOCs are judged by escalation quality, not alert volume
- IR maturity becomes a board, regulatory, and insurance concern
- Cloud, identity, and OT response readiness become harder to defer
The common thread is validation. Organisations will need evidence that plans, playbooks, logging, decision-making, and escalation paths work before a serious incident exposes the gaps.
Need a clearer picture of your organisation’s incident response capability?
If you’re unsure whether your plans, playbooks, and coordination structures would hold up during a real incident, explore our Incident Capability Validation. It’s a fixed-scope engagement designed to baseline and stress-test your response capability before the next serious event.
1. Incident Response Shifts from “Call Us When It’s Burning” to Readiness Roadmaps
The days of calling a digital forensics firm only once the damage is done are fading. More organisations are treating IR as the lifecycle it is rather than an emergency service. Retainer models are evolving from on-call contracts into readiness programmes: regular reviews, playbook updates, tabletop exercises, and continuous tuning.
2. AI-Assisted Triage and Timeline Reconstruction Become Standard
AI-driven tools are getting better at reconstructing complex incident timelines from terabytes of logs, emails, and disk images in minutes, but the differentiator isn’t the AI itself; it’s the human who can interpret, validate, and communicate what those timelines mean. Expert-in-the-loop is going to be around for much longer than most people imagine. It’s not yet possible to replace the expertise of an experienced DFIR professional.
Expect DFIR platforms to embed AI-driven triage and correlation as standard features. However, the real differentiator won’t be the tooling but the organisation’s ability to interpret and validate results.
Teams should train analysts not only to use automated workflows, but to validate evidence, challenge automated conclusions, and maintain evidential integrity throughout an investigation. Automation will accelerate analysis, but organisations that invest in skilled investigators and structured investigation processes will resolve incidents faster and with greater confidence in their findings.
3. SOCs Measured on Quality of Escalation, Not Alert Volume
The “more alerts == better security” mindset is dying. Organisations are realising that efficiency in detection and escalation is a better metric than sheer activity. Mature SOCs will focus on precision: fewer, higher-confidence alerts with faster validation and escalation into structured response playbooks.
Clear escalation pathways, documented investigation steps, and strong coordination between SOC and incident response teams will become essential. Mature organisations will prioritise fewer, better escalations supported by structured response processes, enabling faster containment and clearer communication during incidents.
4. IR Maturity Becomes a Board-Level Metric
Boards and executives are now asking for concrete evidence of readiness: tested IR plans, rehearsed scenarios, and maturity scores. Cyber security will continue its shift from a technical to a governance domain, with IR metrics joining safety and continuity in board packs.
Need a clearer picture of your current readiness?
Our fixed-scope Incident Capability Validation helps regulated and high-consequence organisations baseline, stress-test, and prioritise improvement before committing to a longer-term program.
5. IR Plans and Playbooks Tested Quarterly, Not Annually
The annual tabletop is no longer enough. The pace of change in cloud configurations, team structure, and threat landscape means that IR plans age quickly. Forward-leaning organisations are now running focused, quarterly exercises to validate specific playbooks or crisis communication flows.
6. OT-Aware DFIR in Critical Demand: Talent Gap Persists
Operational technology (OT) environments remain one of the hardest domains for DFIR. The need for analysts who understand both industrial protocols and forensic process is far outstripping supply. As industrial control systems become more connected, this skill gap becomes both a business risk and a safety concern.
Organisations operating critical infrastructure or industrial environments should assume that specialised OT incident response capability will be difficult to source during an emergency. Preparing in advance is essential.
This preparation often includes cross-training internal teams, identifying trusted external responders, and ensuring that response plans account for both IT and OT environments. Waiting until an incident occurs to identify appropriate expertise will significantly delay containment and recovery.
7. Identity Hygiene Failures Overtake Zero-Days as Breach Causes
Compromised credentials and poor identity management will continue to outpace sophisticated exploits. Multi-factor fatigue, over-privileged accounts, and incomplete offboarding remain leading causes of compromise. Attackers exploit predictable human and administrative weaknesses more than technical vulnerabilities.
Organisations should prioritise privilege governance, identity monitoring, and reliable authentication logging, ensuring that investigations can quickly reconstruct who accessed what, when, and how. Without this level of visibility, even well-equipped response teams may struggle to establish the full scope of an incident.
8. Cloud DFIR Maturity Accelerates: IAM and Log Retention Mastery Define Leaders
Cloud investigations are finally catching up with reality. The gap between cloud operations and forensic readiness is closing as teams learn to configure logging, centralise evidence, and automate data preservation. The differentiator will be those who design for investigation from day one.
Effective cloud investigations depend heavily on logging depth, retention, and accessibility during incidents. If critical identity and administrative events are not captured and preserved, investigators may be unable to reconstruct what actually happened. Organisations should review whether critical identity, administrative, and configuration events are logged and retained long enough to support investigations.
9. Cyber Insurance Requires Exercised IR Plans for Coverage
As more actuarial data becomes available, insurers are tightening underwriting standards. Many cyber insurance policies will require not only an incident response plan but documented evidence of recent testing and staff participation. This shift mirrors safety compliance regimes in other high-risk, high-consequence sectors.
Cyber insurers are increasingly looking for evidence that incident response capability has been exercised, not just documented. Organisations should be prepared to demonstrate recent testing of plans, participation from relevant stakeholders, and lessons learned from previous exercises.
Maintaining records of tabletop exercises, plan updates, and training activities will help organisations demonstrate preparedness during policy renewal discussions and may influence coverage terms.
Not sure whether your current plan and playbooks would hold up under pressure?
Start with our Incident Response Plan & Playbooks: 10-Minute Quality Check.
10. The Calm, Well-Rehearsed Teams Outperform the Most Technical
When incidents occur, calm beats clever. The teams that consistently perform best in crises are not those with the deepest technical knowledge, but those with structure, communication discipline, and effective leadership under pressure. Practice, not panic, defines outcomes.
Regular exercises that involve both technical teams and leadership help build familiarity with these structures, allowing teams to operate calmly and decisively when real incidents occur. The organisations that perform best during crises are usually those that have rehearsed their response processes repeatedly.
What Security and Leadership Teams Should Do in 2026
The organisations that perform best during incidents will be the ones that make readiness visible, testable, and repeatable. In practice, that means:
- Baselining current response capability
- Identifying where plans and playbooks break down in real scenarios
- Exercising key workflows quarterly
- Maintaining evidence of readiness for leadership, regulators, and insurers
If you want a lightweight starting point, use our Incident Response Plan & Playbooks: 10-Minute Quality Check.
If you want to rehearse decision-making under pressure, see our Cybersecurity Tabletop Exercises.
And if you need a fixed-scope assessment to baseline and stress-test your capability, explore Incident Capability Validation.
Disclaimer: This content may have been edited or refined with assistance from AI tools. All final content, views, and recommendations are our own.
